In the world of secure communication and data encryption, Pretty Good Privacy (PGP) and GNU Privacy Guard (GPG) are two widely used tools. Both are cryptographic software that provides a means for users to encrypt and decrypt electronic messages, ensuring the confidentiality and integrity of sensitive information. However, there are significant differences between the two. …
In the world of secure communication and data encryption, Pretty Good Privacy (PGP) and GNU Privacy Guard (GPG) are two widely used tools. Both are cryptographic software that provides a means for users to encrypt and decrypt electronic messages, ensuring the confidentiality and integrity of sensitive information. However, there are significant differences between the two. This article explores the distinctions between PGP and GPG, shedding light on their features, compatibility, and usage.
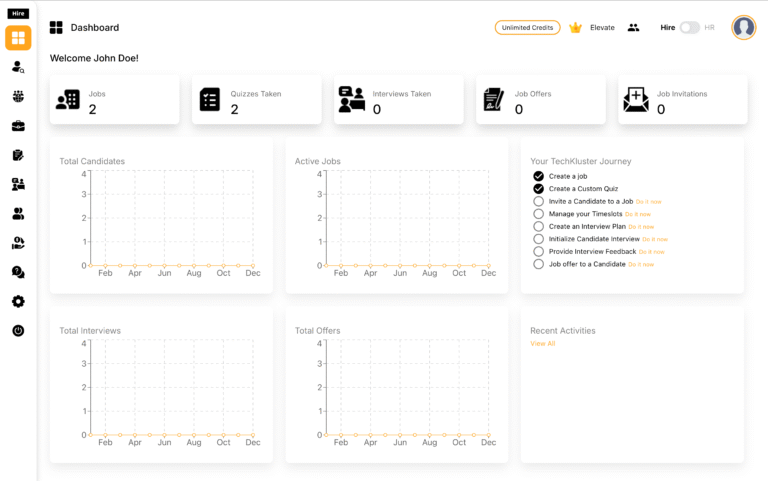
1. Overview of PGP
1.1 PGP Definition
PGP, or Pretty Good Privacy, is a data encryption and decryption program that provides cryptographic privacy and authentication for data communication. It was originally developed by Phil Zimmermann in 1991 and has become a standard for secure communication.
1.2 PGP Features
- Symmetric and Asymmetric Encryption: PGP uses a combination of symmetric-key and public-key cryptography. Symmetric-key encryption is employed for encrypting the actual data, while asymmetric-key encryption is used for exchanging the symmetric key securely.
- Digital Signatures: PGP allows users to sign their messages with a digital signature, providing a way to verify the authenticity and origin of the message.
- Key Management: PGP includes a key management system that enables users to generate, import, and manage their encryption keys.
2. Overview of GPG
2.1 GPG Definition
GNU Privacy Guard, or GPG, is a free and open-source implementation of the OpenPGP standard. GPG is a part of the GNU Project and was developed to provide a free alternative to PGP, addressing some of its limitations and ensuring open access to cryptographic tools.
2.2 GPG Features
- Open Source: GPG is open-source software, meaning its source code is freely available and can be audited by anyone. This transparency enhances trust and security.
- Compatibility: GPG is designed to be compatible with the OpenPGP standard, ensuring interoperability with other OpenPGP-compliant software.
- Multiple Algorithms: GPG supports a variety of encryption algorithms, providing users with flexibility in choosing the most suitable cryptographic methods.
3. Key Differences Between PGP and GPG
3.1 Licensing
One of the fundamental differences is the licensing model. PGP uses a proprietary license, which restricts the distribution and modification of the software. On the other hand, GPG is distributed under the GNU General Public License (GPL), making it free to use, modify, and distribute.
3.2 Software Implementation
While PGP is available as both proprietary and commercial versions, GPG is purely an open-source implementation. GPG’s open nature allows developers to contribute to its improvement and ensures a higher level of transparency.
4. Usage Examples
Let’s look at a simple example of encrypting and decrypting a message using both PGP and GPG.
4.1 PGP Example
# Encrypt a message using PGP
$ gpg --recipient recipient@example.com --encrypt plaintext.txt
# Decrypt the message
$ gpg --decrypt encrypted.txt4.2 GPG Example
# Encrypt a message using GPG
$ gpg --recipient recipient@example.com --encrypt plaintext.txt
# Decrypt the message
$ gpg --decrypt encrypted.txt5. Security Considerations
5.1 Security Models
While both PGP and GPG offer robust security features, their underlying security models differ. PGP relies on a web of trust, where users validate the authenticity of each other’s public keys. GPG, being an open-source tool, emphasizes a decentralized model that encourages peer review and collaboration. The choice between these models often depends on user preferences and the specific security requirements of the environment.
5.2 Algorithm Support
Another crucial aspect is the support for encryption algorithms. PGP traditionally uses the RSA algorithm for public-key cryptography, while GPG supports a broader range of algorithms, including RSA, ElGamal, DSA, and more. The ability to choose from multiple algorithms allows GPG users to adapt to evolving security standards and preferences.
6. Compatibility and Interoperability
6.1 OpenPGP Standard
Both PGP and GPG adhere to the OpenPGP standard, ensuring a level of compatibility between the two. Messages encrypted with PGP can typically be decrypted with GPG and vice versa. This interoperability is essential for users who may need to communicate securely with others using a different implementation.
6.2 Cross-Platform Support
Both PGP and GPG provide cross-platform support, making them accessible on various operating systems, including Windows, macOS, and Linux. This flexibility allows users to maintain secure communication across diverse computing environments.
7. Community Support and Development
7.1 Community Engagement
The PGP and GPG communities play a vital role in the ongoing development and improvement of these tools. PGP, with its commercial and proprietary history, has a more centralized development process. In contrast, GPG’s open-source nature encourages community involvement, leading to a diverse range of contributors and perspectives.
7.2 Update Frequency
GPG, being open source, often benefits from more frequent updates and improvements driven by the collaborative efforts of the community. Users can take advantage of the latest security patches and features promptly. PGP, being commercially driven, might have less frequent updates, potentially impacting its responsiveness to emerging threats.
While PGP has a long history and has been a stalwart in the field of encryption, GPG’s open-source nature and compatibility with the OpenPGP standard make it an attractive choice for those who value transparency and community-driven development.
Ultimately, users should evaluate their specific needs, consider the trade-offs between proprietary and open-source models, and choose the tool that aligns best with their security principles and operational requirements. Whether encrypting emails, files, or entire disk partitions, the goal remains constant: safeguarding sensitive information in an increasingly digital and interconnected world.