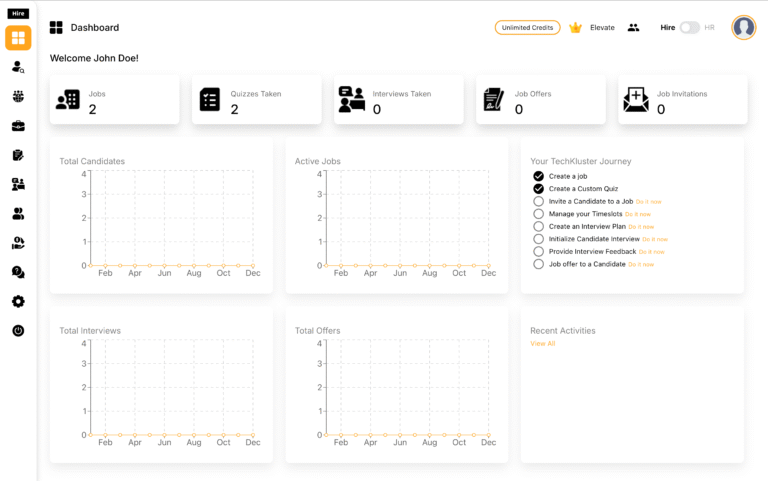
Introduction The chmod -R 777 / command is a powerful and potentially destructive operation in Unix-like operating systems. It is used to change the permissions of all files and directories within the root directory ("/") to full read, write, and execute access for everyone. While it may seem like a quick solution to permission issues, …
Introduction
The chmod -R 777 / command is a powerful and potentially destructive operation in Unix-like operating systems. It is used to change the permissions of all files and directories within the root directory (“/”) to full read, write, and execute access for everyone. While it may seem like a quick solution to permission issues, using this command poses serious security risks and can lead to unintended consequences.
The chmod Command
Before delving into the dangers of chmod -R 777 /, let’s briefly understand the chmod command. chmod is a command-line utility that allows users to change the permissions of files and directories in Unix-based systems. The command is followed by a three-digit numeric code or symbolic representation to specify the desired permissions.
- The first digit represents the owner’s permissions.
- The second digit represents the group’s permissions.
- The third digit represents others’ (everyone else’s) permissions.
Each digit is a combination of read (4), write (2), and execute (1) permissions. For example, chmod 755 file.txt grants read, write, and execute permissions to the owner, and read and execute permissions to the group and others.
The -R Option
The -R option in chmod stands for recursive, meaning that the command will be applied to all files and directories within the specified directory and its subdirectories. When used with the root directory (“/”), it affects the entire file system.
Dangers of chmod -R 777 /
1. Security Risks
Granting full read, write, and execute permissions to everyone on the system is a significant security risk. It allows any user or program to modify critical system files, leading to potential vulnerabilities and unauthorized access. Malicious actors could exploit this openness to compromise the system’s integrity.
chmod -R 777 /2. Data Loss
The chmod -R 777 / command can result in unintended data loss. By changing permissions indiscriminately, users may accidentally alter or delete crucial system files, leading to system instability or failure. Critical configuration files and directories necessary for the operating system’s functionality may become compromised.
3. Impact on System Performance
Granting excessive permissions to all files and directories can impact system performance. Unrestricted access might allow unnecessary modifications or executions of processes, leading to increased resource usage and potential performance degradation.
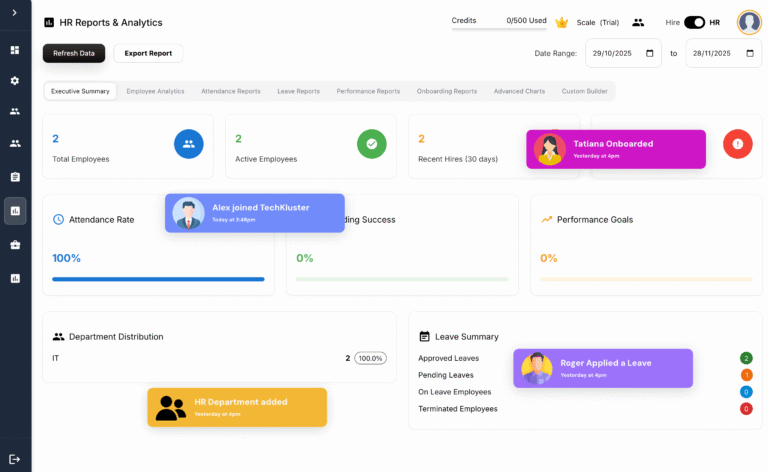
Best Practices for File Permissions
Instead of resorting to the potentially destructive chmod -R 777 / command, it is advisable to follow best practices for managing file permissions. Only grant the minimum necessary permissions to users and groups, and avoid providing global access unless absolutely required.
# Example: Grant read and execute permissions to the owner, and read-only to others
chmod -R 755 /path/to/directoryNow that we understand the dangers associated with chmod -R 777 /, let’s explore alternative approaches to mitigate these risks and maintain a secure system.
1. Specific Directory Permissions
Rather than applying changes to the entire root directory, it is advisable to target specific directories or files that require modified permissions. This approach allows for a more granular control of access rights, minimizing the potential impact on critical system components.
# Example: Grant read and write permissions to a specific directory
chmod -R 600 /path/to/sensitive_directory2. User and Group Management
Proper user and group management can significantly enhance system security. Assigning files and directories to specific users or groups, and carefully managing their permissions, ensures that access is restricted to authorized individuals or processes.
# Example: Assign a file to a specific user and group
chown username:groupname /path/to/file
chmod 640 /path/to/file3. Regular Backups
To mitigate the risk of data loss resulting from accidental changes or deletions, regular backups are essential. Implementing a robust backup strategy ensures that critical data can be restored in the event of unintentional modifications caused by incorrect permission changes.
4. Audit and Monitoring
Regularly audit and monitor file permissions to identify and rectify any anomalies promptly. Automated tools and scripts can assist in tracking changes and alerting administrators to potential security issues.
5. Limited Use of Wildcards
Exercise caution when using wildcards with chmod, especially in conjunction with the -R option. Wildcards such as ‘*’ can match a large number of files, potentially leading to unintended consequences. Always double-check the list of affected files before applying changes.
# Example: Use with caution and verify the files matched by the wildcard
chmod -R 644 /path/to/files/*While the chmod -R 777 / command might seem like a quick fix for permission-related issues, it poses severe risks to system security and stability. By adopting a more selective and cautious approach to permission management, administrators can maintain a secure environment while minimizing the potential for unintended consequences.